post
It’s often said that passwords are weak, and that to be secure they must be “complex”. What does this really mean and is there any truth to it? The reality of a password is it is a single point of protection between a bad guy and your sensitive information, so there is no doubt of its importance, but how strong is a password?
Passwords, are as it says on the tin, a “pass-word” something you can remember that no one else knows. This is fine in principle, but the premise is out of date. The premise that a single word can suffice to protect your sensitive data is no longer true, although to be fair to the principle, a long time ago it was a perfectly adequate protection. So why has this changed?
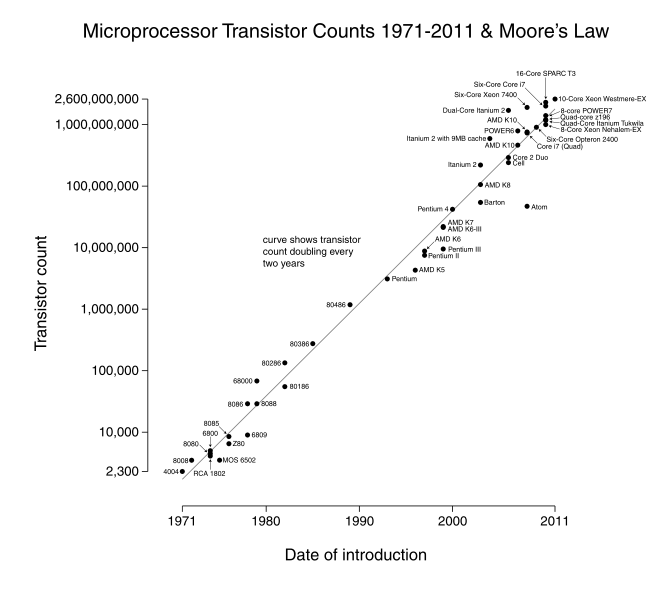
“Moore’s Law” is the answer. Essentially, Moore’s Law is the principle that every 2 years the power of computing hardware doubles through innovation and technological progression, and this has been proven to date. As a result of this, the base premise that I, a human, can’t reasonably guess a “pass-word” in any sensible amount of time, with nothing else to go on for clues, is clearly finished.
The reason behind this demise is that Moore’s Law has allowed the computer to be used as an attack tool against the humble “pass-word” and as we know, computers do things a little bit quicker than us. To put this in perspective, a humble dictionary based “pass-word” as per its original design can be guessed by your average desktop computer in minutes or less. That’s any word in the English dictionary to be clear.
So to answer this problem, IT specialists and Security folk decided that the best idea was to complicate words with additional characters that would stop this kind of attack and force bad guys to do it the hard way, also known as “brute-force cracking”. This approach is less elegant than the prior attack as it requires the brute force application of trial and error! Essentially, every possible combination of letters, numbers & special characters has to be tried to guess your password. The length of the password has to be multiplied by the combinations possible, both by quantity of characters in the password (length) and potential characters that could have been chosen from (character set).
In the case of an all lower case password, the character set is only 26, however, if you use Upper and Lower case, you get 52, add in numbers 0-9 and that makes it 62, then for added super complexity, and the average IT persons requirements, add in the complete extended special character set from a standard PC (33 or more), and you get a pretty big character space to work with!
Typically, these requirements are stated as a minimum of 8 characters, using upper and lower case, at least 1 number, and 1 special character. Something like this is, I believe, what they are hoping for:
T4$cwPQs
So on face value this additional complexity requirement on the password seems to be the right solution as it makes the potential brute force attacks on a password a lot harder to perform and therefore the passwords more secure.
The big problem of course here is that humans are not computers, and our ability to remember, obscure combinations of letters, numbers, case and special characters is limited to all but a few special cases (myself included)! As a result of this, the added complexity only serves to frustrate, annoy and cause us humans to do what we do best, work around the system! A great example of an insecure, secure password is this:
Pa$$word1
It meets the complexity requirements, but is easily guessable so defeats the objective. Other good examples of this tend to involve number plates, family names and pet names etc, all using common character substitutions based on similarity of shape.
So let’s test the theory a little. The following data is the example time to brute force a password based on a “typical” desktop PC:
| Password | Time to Crack |
| Hello | 0.002970344 seconds |
| T4$cwPQs | 3 days |
| Pa$$word1 | 275 days |
Notice in the table above, that the password used as an insecure example actually turned out more secure than the one that was hard to remember? That’s simply because it was 1 character longer! Yes, that’s right, just 1 more character on that length made that kind of impact.
This is the revelation that is often overlooked by the IT specialists who are so invested in the “way things are” vs those that are looking to the way things could be.
What most people don’t realise is that length is much more important than character-set in the context of a password. As long as you’re dealing with at least 26 characters, i.e all lowercase, or even better, upper case too, you can get some pretty astonishing results, just by switching from a “pass-word” to a “pass-phrase”
Let’s look at what that does to our table:
| Password | Time to Crack |
| Hello | 0.002970344 seconds |
| T4$cwPQs | 3 days |
| Pa$$word1 | 275 days |
| helloworld | 9 hours |
| HelloWorld | 1 year |
| HiMyNameIsJay | 161 thousand years |
| todayisabrightsunnyday | 106 trillion years |
| TodayisaBrightSunnyDay | 447 quintillion years |
Now, I am no rocket scientist, but that’s the first time I have ever seen the word “quintillion” and am pretty sure, it’s going to keep my sensitive data safe!
Now, before we all jump and change our passwords to pass-phrases, there are some gotchas to consider. Firstly, A number of attacks exist that surpass Brute Forcing approaches, such as hybrid attacks that combine multiple attacks into a better statistical approach, and then the dreaded “rainbow Tables”.
Rainbow Tables are essentially a brute force attack that someone wrote down. What I mean by this is a brute force attack try’s every possible combination of password to guess it every time it’s run. A Rainbow table is a file that contains every possible brute force combination, already written down, so all you have to do is search through it for your encrypted password to find a match. This is a much quicker approach. So much so that it can do ANY combination of upper, lower, number & special character passwords up to 14 characters long in a matter of minutes!
So again, we come back to the length point. “If my pass-phrase is longer than 14 characters then I am ok?” This is true, but Rainbow tables are continuously improved upon so go for a long passphrase to be safe.
The final gotcha, is that as the industry of IT experts hasn’t quite got their head around this concept yet, not everyone will “let” you use this simple approach and will force you to have a counter-intuitive, easy to crack “complex password”.
So my advice is to use a phrase whenever you can; and where you can’t, make it as long and easy as you can to remember it!
Visit our website at www.justasc.net for more information on the services we provide or call us on 0845 6437406 for a free consultation and to learn more about the current threat landscape.